How to Ensure Internet Privacy Protection
Will Simonds
Reading time: 11 minutes

Table of Contents
With online scams, identity theft, and data breaches on the rise, now more than ever, people have expressed concern about their Internet privacy.
But even though there’s a general worry, a recent survey showed that as many as 46% of respondents had no idea where to begin to protect sensitive information they share online, and 38% didn’t know what to do to secure their data.
In this guide, we will show you how to take control over your own digital privacy and keep your information safe. From defining and differentiating numerous key terms, to analyzing the major issues affecting privacy today, we’ll outline the problems and provide you with solutions.
Internet privacy vs. online security
Internet privacy (also “online privacy”) is the protection of personal privacy when you store, display, or provide information online. Whether it’s personally identifiable information (PII), or details about online behavior, it’s your right to know how and where it’s stored or displayed.
Online security, on the other hand, refers to the tools and resources that are available to protect your online identity and data. These resources might include antivirus software, secured personal devices, or web services, among other things.
While online security is simply protecting your data against unauthorized access or malicious attacks, internet privacy relies on the proper usage, handling, processing, or storage of your personal information, and is therefore more often compromised.
For example, when you sign up for an ecommerce platform, it’s likely your online security is easily maintained. At the same time, however, your privacy might be compromised because ecommerce sites often sell consumer information to third-party marketers.
Although it might not sound like a big deal, the risks associated with jeopardizing your online privacy to any degree can be severe.
The major risks of compromised Internet privacy
While several risks come with compromising your online privacy, information used to track your behavior, scam you, or, in the worst case scenarios, steal your identity, can be among the most damaging.
1. Identity theft
If enough of your personal information is compromised, it can lead to identity theft. Your information can be used to make online purchases, apply for loans or credit cards, even claim unemployment benefits.
Dealing with the fallout from a case of identity theft is extremely stressful, and can be very costly. It may take a long time to regain your reputation or restore your credit rating.
2. Online scams and fraud
There are many different kinds of online scams, such as spam texts or robocalls, that pose as banking institutions or government agencies. The more information that is available about you on the Internet, the more sophisticated the frauds can be.
3. Doxxing
Doxxing (or doxing) is the practice of having your identity, or sensitive personal information, exposed without your permission.
It became widely known as a revenge tactic hackers used to reveal identities of rivals, but has become most commonly used to harass, intimidate, or punish victims. Public figures, reporters, and gamers are often targets, but anyone with compromised online information is at risk.
4. Tracking
Companies called data brokers operate with the singular purpose of tracking everything one does online, creating a profile, and making a profit by selling it.
Data broker methods of harvesting online data include the exploitation of cookies, mobile apps, and public records, or simply trawling the web. Even if you’ve never shared personal information yourself, websites you visit regularly combined with public record can create an accurate profile.
When this information is made available to the highest bidders for purchase, oftentimes that means third-party marketers, which results in you receiving junk mail, robocalls, and spam texts. It also exposes you to multiple risks and privacy breaches.
A privacy strategy to protect you across the Internet
The data trail you leave behind goes deeper than just the information you’re posting yourself. In order to protect your Internet privacy from tracking, scams, doxxing, or identity theft, you need a thorough online privacy strategy that can also get at the root of the problem.
1. Remove your personal information from data brokers
Because data brokers are perhaps one of the main reasons your personal information gets compromised in the first place, removing yourself from each and every one of these databases is an essential step to protecting your Internet privacy.
To do that, your profile needs to be deleted from each data-broker platform individually, and you’ll be surprised to learn just how many of them exist (hint: it’s hundreds). You can go through the process manually using our free DIY opt-out guides, or you can sign up for a service.
While the opt-out process is straightforward, it can be very time consuming. On top of that, data brokers are notorious for re-listing profiles even after they’ve been removed. Therefore, these databases need to be constantly monitored to ensure your personal data remains removed.
Using a professional data-removal service like DeleteMe to remove and monitor your personal data on an ongoing basis is a much easier and more effective option.
2. Secure your social media accounts
Now, it’s true you can’t control what information others post about you online, but you can control what you post yourself. Take a moment to consider what information you reveal on social media and ask yourself: does anyone really need to know these things?
Set your social media profiles to “private,” use a nickname, untag yourself from photos, and delete content that may reveal too much personal information. It’s also a good idea to delete accounts no longer in use. If you can’t delete them, remove as much content as possible.
Furthermore, some social media platforms are capable of tracking real-time location, even if they’re not actively being used. This is a huge privacy concern, but you can disable the location tracking setting across all of your devices. Here’s how:
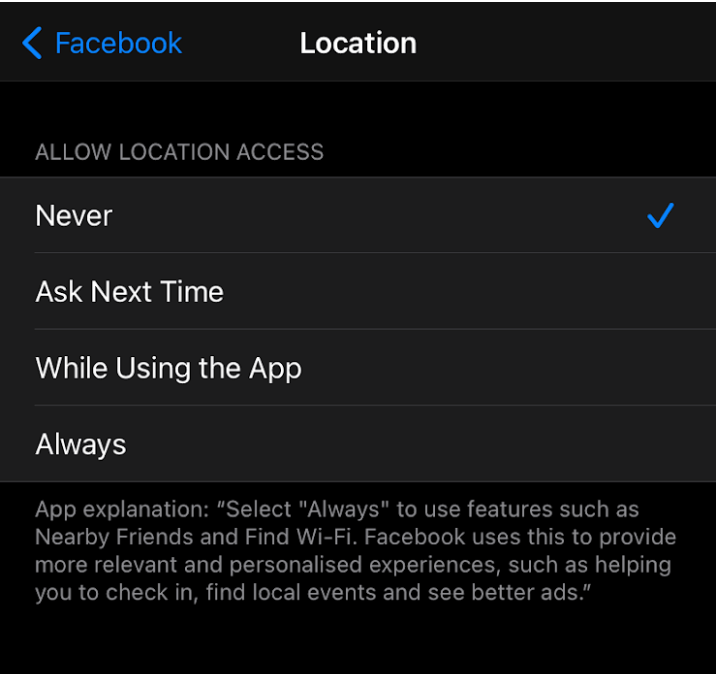
Disable location tracking on iPhone
- Go to “Settings”
- Scroll down, press “Facebook,” “Instagram,” “Twitter,” or other social media app
- Press “Location”
- Choose “Never”
Disable location tracking on Android
- Go to “Settings”
- Scroll down, click “Manage Apps” (on some devices, you must first click “Device Manager”)
- Click “App Settings” or “App Configurations”
- Click “Permissions”
- Click “Your Location”
- Disable all apps that you don’t want to access your location
Please note: you may need to edit these settings on both desktop as well as mobile devices.
3. Fortify your passwords with a password manager
Another important step is being smarter with password choice. Change them regularly, and if you’re currently using the same password across many different devices and sites and you think they’re secure, you might want to think again.
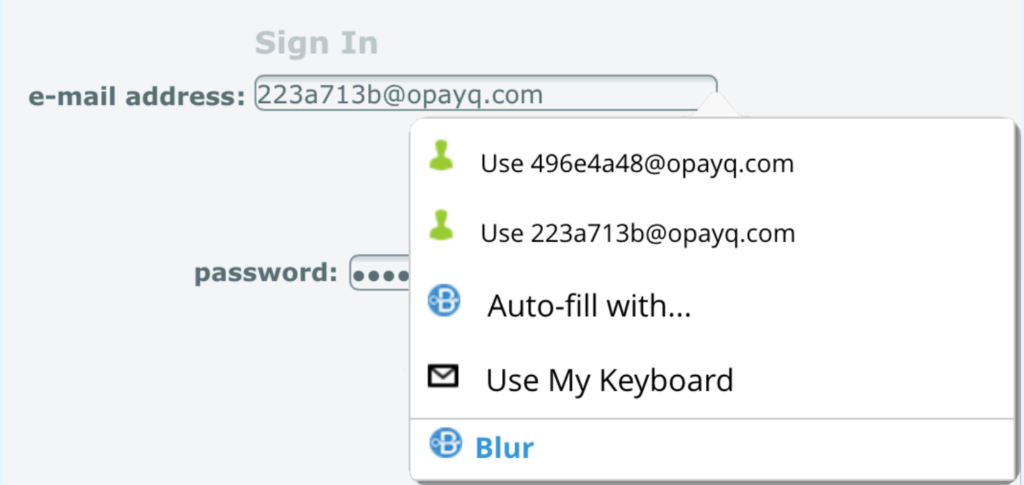
Using unique passwords for every account is the key to keeping your personal information safe. If it’s too much to remember them all, your best option might be to use a password manager like Blur to generate strong passwords and keep them all safely in one place.
4. Use a VPN
A virtual private network (VPN) reroutes your IP address, and disguises and encrypts your browsing traffic while you surf the web. It’s a great way to protect your privacy, especially when using public WiFi (try to avoid them as much as you can). With a VPN, your browsing activities can’t be monitored and it will keep both marketers and hackers at bay.
There are plenty of free VPNs to choose from, but carefully read privacy policies and customer reviews. Paid VPNs generally provide more robust security and clearer privacy standards. Also, choose a “no log” VPN, which means the provider doesn’t track your internet activity.
5. Change to a private browser and email provider
A private browser won’t track your activity and you’ll be able to use the Internet without cookies, temporary files, or a browser history being saved. Chrome’s “Incognito” works, but only to some extent. Options we recommend are DuckDuckGo, Brave, or Blur Private Browser (for iOS).
The same is true for email. Account providers like Gmail and Yahoo monitor the content of user emails for marketing and advertising purposes. A private email provider like Fastmail or ProtonMail is a much safer option.
However, if it’s too big of a hassle to change email addresses, you can always use Blur’s masked email when signing up with any online platform. Using this, your email will still work as usual, it just can’t be tracked back to you or sold forward for marketing purposes.
6. Use secure mobile apps that won’t sell your data
Many apps (especially free ones) make money by selling your data (which is why you should read carefully when you sign up). For example, dating apps like Tinder and Grindr are known for collecting and selling huge amounts of data and compromising Internet privacy.
Always review app terms of use, and check privacy settings both in apps and on your device.
You have the option to deny an app’s ability to track you by disabling the tracking feature, particularly on an iPhone. Here’s how: Go to Settings > Privacy > Tracking > disable “Allow Apps to Request to Track.”
Additionally, delete all apps you no longer use or need. The best way to do this is to contact the app admin directly and ask them to remove your information before deleting it.
7. Never click on suspicious links
It’s more likely that an email from a trusted institution, like your bank, that asks you to “click a link,” “download an attachment,” or “share sensitive personal information online,” is actually a phishing scam, and not what it claims to be.
Pay close attention to a sender’s email address—if it’s different from the address of the company, it’s most likely a scam. Other giveaways are spelling or grammar errors in the text, as well as unusual phrasing that sounds like it was written by a non-native speaker.
Also beware, these suspicious links don’t only happen via trusted institutions. In fact, they can easily be shared through other senders as well, even a close friend! If a friend’s account was hacked, it’s possible fraudsters are trying to get connections to open malicious links.
It’s better to be safe than sorry, and confirm with either an individual or an institution if an email or text containing a suspicious link was sent to you on purpose or not at all.
8. Use two-factor authentication whenever possible
Two-factor authentication (2FA) is an additional security measure on top of the protection of a conventional account password.
The most common form of 2FA is a simple SMS verification when you attempt to log into an online account. While this is considered acceptable for most Internet sites, for anything enabling online payments, additional security measures should be used.
Using 2FA whenever possible is a good addition to your internet security, and, of course, always remember to log out of all platforms when you’re finished using them.
DeleteMe and digital privacy
Now you have a better idea about why online privacy matters, and how you can take measures to protect your own Internet privacy.
Not knowing how your online information is being used probably makes you feel a little vulnerable and unsafe, and that’s not how it should be. Remember, you have the right to Internet privacy, and you need to protect that right.
If you feel your information has been misused, you can report it to the American Civil Liberties Union (ACLU), the Electronic Privacy Information Center (EPIC), the Electronic Frontier Foundation (EFF), or get in touch with us.
At Delete Me, we’re experts at removing personal data from the Internet, and are committed to raising awareness about the importance of online privacy. Our mission is to provide you with the tools and information that will keep you and your family’s information safe.
Let our team of privacy experts work for you, with plans that start at just $10.75 a month.
Our privacy advisors:
- Continuously find and remove your sensitive data online
- Stop companies from selling your data – all year long
- Have removed 35M+ records
of personal data from the web
Save 10% on any individual and
family privacy plan
with code: BLOG10
news?
Don’t have the time?
DeleteMe is our premium privacy service that removes you from more than 750 data brokers like Whitepages, Spokeo, BeenVerified, plus many more.
Save 10% on DeleteMe when you use the code BLOG10.

















