A Guide to Doxxing Yourself On the Internet
Laura Martisiute
Reading time: 8 minutes

Table of Contents
It might seem counterintuitive, but the best protection against being doxxed (or “doxed” or getting “docs dropped”) is to follow a guide to doxxing yourself on the internet.
By trying to find information about yourself online, you’ll be able to see how easy it would be for someone else to do it – and then take steps to make yourself less doxxable.
How to Dox Yourself
Follow the following seven steps to dox yourself.
Tip: Want to learn more about doxxing in general? Read about how doxxing happens.
1. Google yourself
Chances are, the first thing that anyone who wants to dox you will do is search for your name (or username, phone number, etc.) on Google.
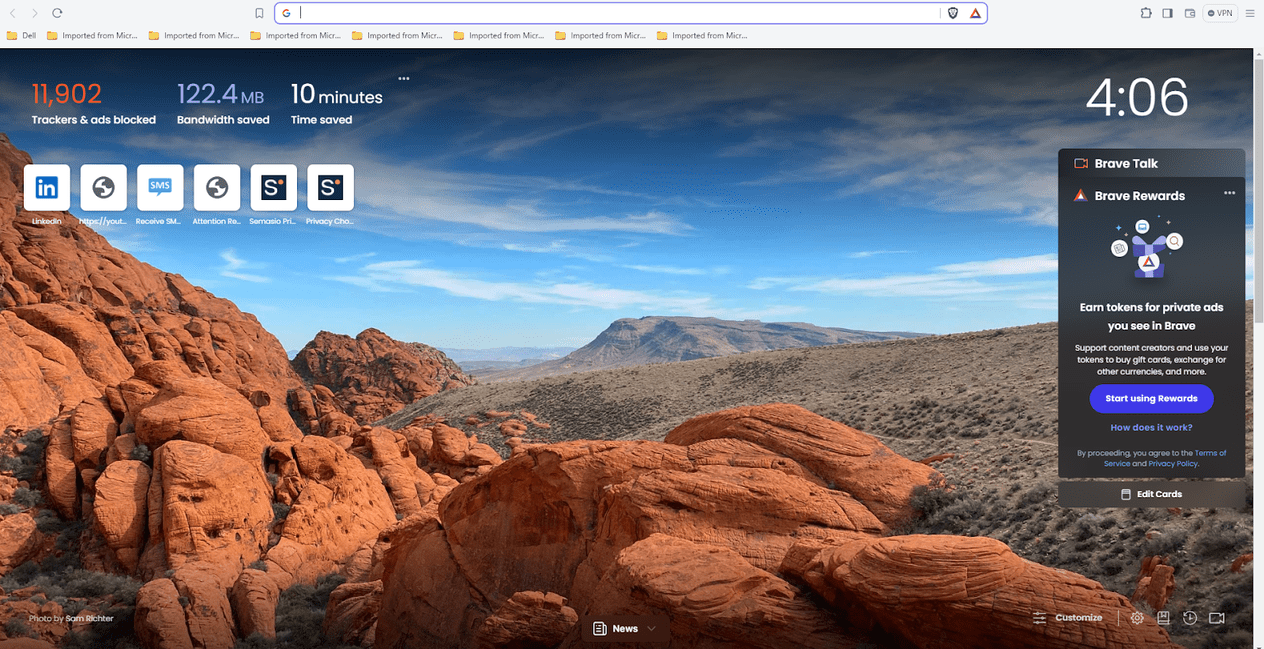
Keep in mind that you’ll need to open a private tab or go into incognito mode to avoid seeing customized results.
You might have to put your name in quotation marks or add geographical details to get an accurate result. Think about what someone who is trying to dox you may already know – your name, phone number, the city you live in. Include anything that may be public information.
For most people, social media profiles will be the first few results that show up, but you could also see listings from data brokers (people search sites), personal websites, public records, and so on.
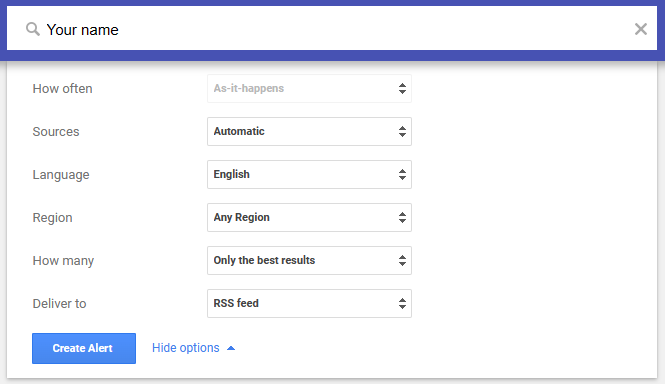
You can set up Google Alerts to be notified when new information appears about you online. To do that:
- Go to Google Alerts.
- Type in your name (or other personal data) in the search bar.
- Click “Show options” to change how often you get notifications, what sites you want to see, the part of the world you want information from, etc.
- Click “Create Alert.”
To learn more, read our guide on how to remove doxxing content on Google.
2. Find yourself on social media
Open up a social media site where you have an account (such as Facebook, X, Instagram, Reddit, or LinkedIn), log out, and run a search for your name (adding in your location if needed to refine the results).
Once you’ve found yourself, take note of what personal data is visible. Could someone see what you look like? Could they learn where you work, where you like to eat, who your family members are? Even information that might seem insignificant, like your pet’s name or the fact that you speak American English, can help someone build up an accurate picture of your life.
If you use the same username across multiple social media platforms, forums, or apps, then anyone who has found you on one platform can easily discover every other account you have – making you vulnerable to online harassment, social engineering, death threats, and more.
Tip: Learn how to report doxxing on various different platforms, including X/Twitter (plus, here’s Twitter’s doxxing policy).
3. Look for yourself on people search sites
Data brokers and people search sites are companies that collect your personal information from a range of sources, compile this information into comprehensive profiles, and then sell these profiles to pretty much anyone who wants to buy them.
If your search engine results include data brokers (such as Whitepages, Spokeo, PeekYou, or PeopleSmart), follow the link to see what they have on you.
Depending on the website, data brokers can give results based on very little information. If someone knows your full name, they can start with that, but they can also do a search based on your username, phone number, home address, or email to find out more about you.
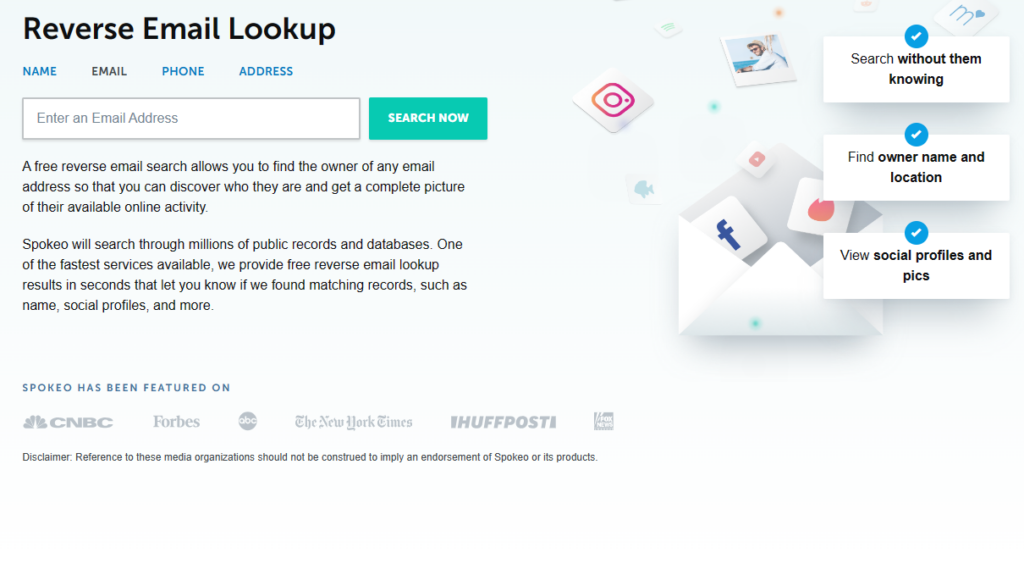
To be thorough, try doing a reverse search on all your identifying details.
Note that not all data brokers and people search sites will show up on Google Search results when you type in your name, even if they have your personal details.
For this reason, you should go to each major data broker and people search site and type in your details into their search bar rather than relying on Google (or some other search engine, like Bing) alone.
If you find that a data broker has your information, you can, in most cases, opt out of their database. However, this is where things get tricky. The opt-out process differs from one data broker to the next – while some data brokers let you opt out via an online form, others might request that you send them an opt-out request through email instead.
Unfortunately, data brokers refresh their databases when they collect more data about you, so you’ll need to repeat this process.
If you’d rather not have to opt out of data brokers manually, consider using a data broker removal service like DeleteMe, where our privacy experts remove you from data broker databases on your behalf.
4. Check what your website says about you
If you have a personal website, assess it objectively: do you overshare by including private information or contact details?
Website owners should also keep in mind that their contact info could be visible using the Whois lookup tool. Do a search on your domain and see if your name, home address, and other information is included. If it is, contact your domain registrar and enroll in private registration.
Remember that even if you’ve deleted your website, it may still be accessible through the Internet Archive.
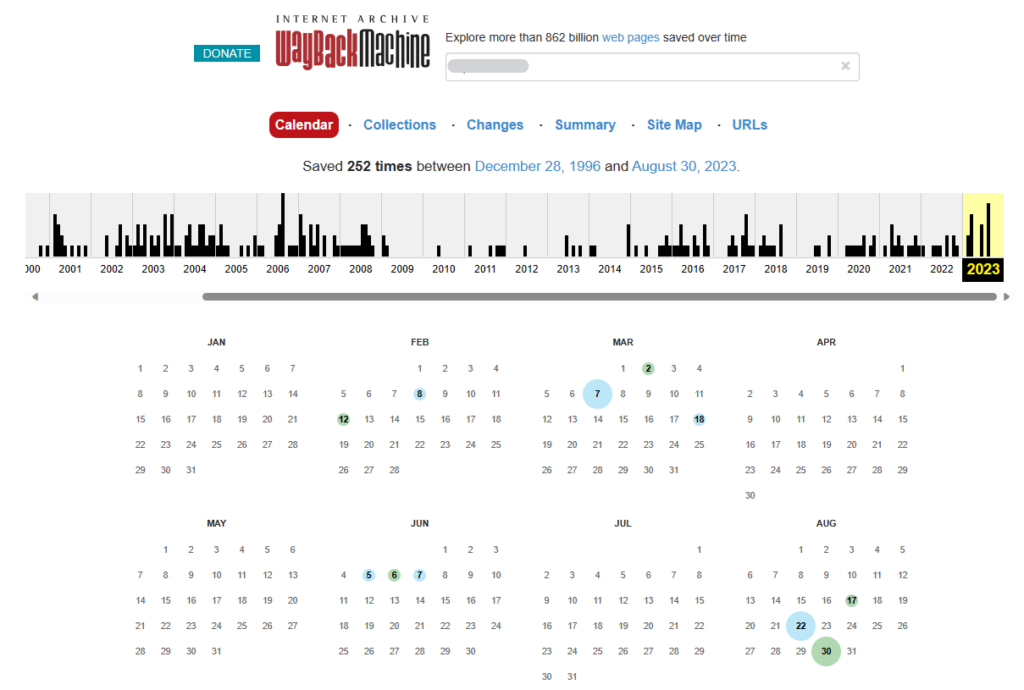
If it is, you may be able to have it taken down, though the results are mixed.
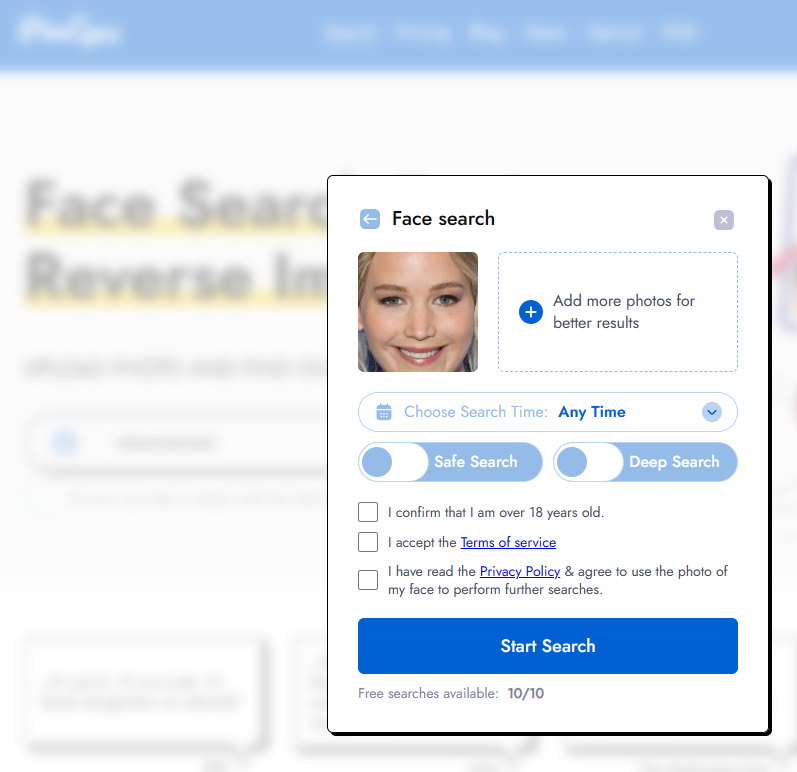
5. Do a reverse photo search
Through a reverse image search, anyone with a photo of you can see where else that particular photo and similar photos appear online.
There are several ways someone might perform a reverse photo search. For instance, they may Google your name in Google Images, right-click on your image, and then select “Search the web for image” to find where else your photo shows up online.
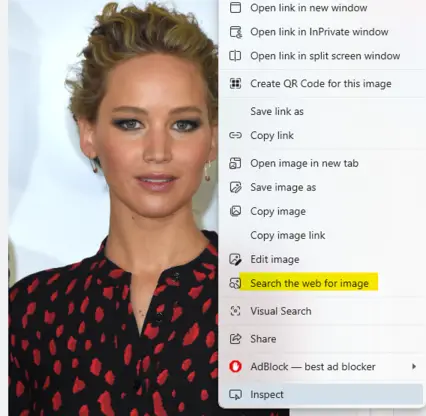
Or, they may upload an image of you they found somewhere else (social media account, newspaper, etc.) onto Google Lens – for example, your profile image.
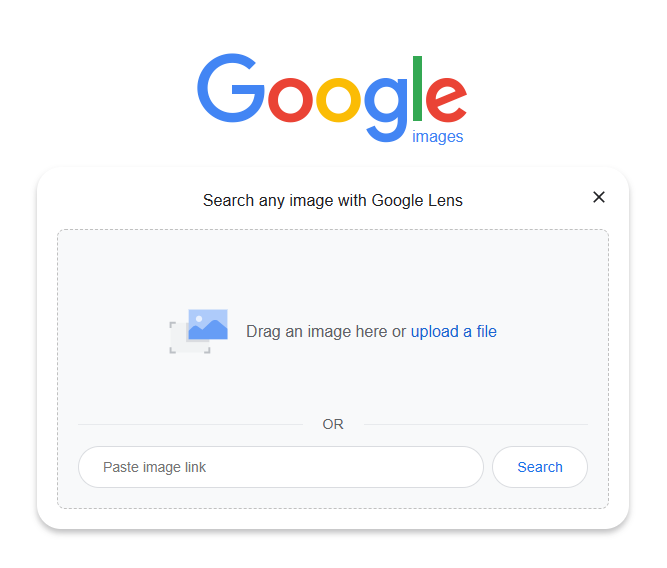
That will cause a sidebar to pop up on the right, where Google Lens will scan the internet for the photo. Click “Find Image Source” at that point to see where the photo is posted online – potentially showing all other accounts you’ve uploaded the same profile picture to.
There are also reverse image search tools like PimEyes and TinEye that can do the same function.
I found PimEyes to be especially good. When I uploaded my own (public) photo, it returned results of where else that photo appears online – plus similar images, including a picture of me in a local newspaper from a work event years ago that I had totally forgotten existed.
6. See if you appear in any data breaches
If your information has been involved in a data breach, there’s a good chance someone will be able to find it on the dark web. Data breaches can include a wealth of sensitive information about you, including your online account login details, social security number, and more.
You can find out if your data was part of a breach by going to the Have I Been Pwned online tool and searching for your email address.
If it comes back positive, you should change the passwords associated with the breached accounts and any other accounts that use the same password.
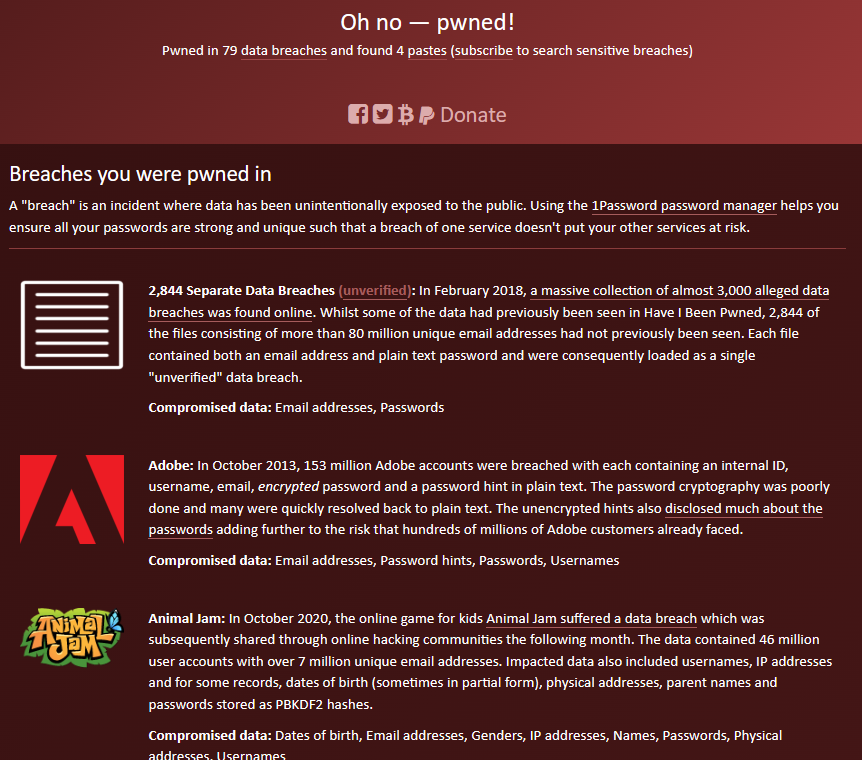
Going forward, using two-step authentication and a password manager can protect your accounts from being accessed after a breach occurs.
7. Review your professional presence
If you’ve ever applied for work through a website or uploaded your resume to the internet, your private information may be sitting in plain view.
To find out if your resume or CV is floating around, go to Google and type in the search string “[First Name] [Last Name]” filetype:pdf (including the quotation marks).
That will come back with any PDFs associated with your name (if there are any).
If it’s a PDF on a site you have access to, make sure to revise it if it has your contact information (phone number, email address, etc) on it.
Become Undoxxable
The less information exists about you online, the less likely it is that someone will be able to doxx you. For best results, doxx yourself continuously (use our list of doxxing tools to help you) and share as little about your life on the internet as possible.
For more information, read our guide on how to prevent doxxing.
Our privacy advisors:
- Continuously find and remove your sensitive data online
- Stop companies from selling your data – all year long
- Have removed 35M+ records
of personal data from the web
Save 10% on any individual and
family privacy plan
with code: BLOG10
news?
Don’t have the time?
DeleteMe is our premium privacy service that removes you from more than 750 data brokers like Whitepages, Spokeo, BeenVerified, plus many more.
Save 10% on DeleteMe when you use the code BLOG10.